
It’s unfortunately been a busy year for phishing scammers thanks to the pandemic. In April 2020, the Canadian Press reported a 4000% increase in ransomware phishing emails alone.
Now, on top of the COVID-related phishing are the seasonal attacks that come in around the holidays to further threaten network security.
Phishing remains the preferred delivery vehicle for viruses, ransomware, trojans, and multiple other threats. This necessitates strong and ongoing employee awareness training to help users identify and avoid being taken in by dangerous emails.
The two main areas of seasonal employee phishing awareness training are:
Below, we’ll go through the types of holiday-themed phishing attacks employees can expect to see in their inboxes this time of year, and the best practices they should follow to avoid causing a malware infection or data breach.
This is the time of year that companies email out holiday schedules, so their customers know what days they’ll be closed. This gives phishing scammers a great cover for sending a macro-enabled Word document or a link to a site that does a drive-by download of malware.
While holiday parties are going to look completely different this year due to the coronavirus pandemic, many businesses are still planning to do something to show employees are appreciated.
So, it may not seem unusual for an employee to receive an email in their inbox asking them to take a holiday survey about what the company should do this year.
This is a common phishing scam and can lead to an infection of ransomware or other malware.
Order emails that look identical to those from Amazon and other retailers are a common holiday phishing scam.
The scammer is counting on an immediate emotional response from a recipient which may be:
In any of the above scenarios, the goal is to get the user to click on the email to learn more before they realize it’s a fake.
The bogus tracking notification is another common scam that hides among all the legitimate tracking emails that come due to increased online shopping this time of year.
These phishing scams also will often exactly match the look, logo and all, of a legitimate shipper to fool the recipient into believing it’s real. They may also even use the shipper’s website domain in the “From” line.
Another type of holiday phishing attack to be aware of is the sale email that offers rock-bottom prices and seeming steals on popular electronics and other gifts.
These types of scams are usually used to steal the victim’s payment card information.
88% of phishing emails use links to dangerous sites rather than file attachments. This is an example of how the attack methods change to get around email protections that block malicious file attachments.
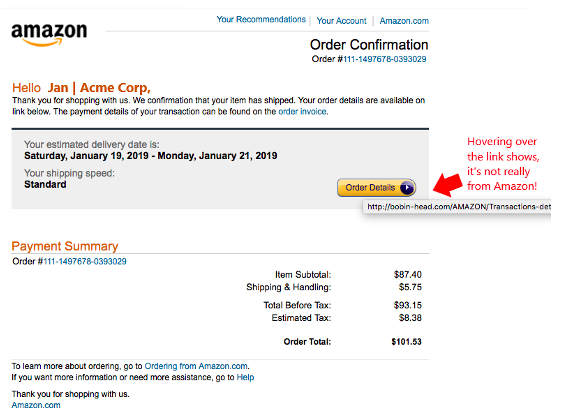
It’s a good rule of thumb to always hover over any email links before clicking on them. This will reveal the real URL and it’s often the fastest way to spot a phishing email.
You can avoid getting tricked into clicking a link in a fake tracking or order email by never checking on orders by email link. Instead, go directly to the retailer or shipper’s website by typing the address in the browser. Then check on any purported orders or tracking directly.
If you don’t see any information about the order or tracking on the legitimate retailer/shipper’s website, then the email is most likely a phishing attack.
One way that scammers trick employees into opening those holiday schedule or holiday survey emails, among others, is to use a legitimate email address in the “From” line of a message.
Employees aren’t always aware that a phishing scammer can type whatever they like in that address, but it doesn’t mean that address actually sent the message.
This is called email spoofing and it’s used often in phishing attacks to gain trust for a message.
Avoid falling prey to this and always double check a message by phone or in person. For example, check with your administrative team or manager to see if the company really did send out a survey about holiday festivities before you take any kind of action on the email.
When an email comes in that is not expected, it’s best to always take a stance of suspicion and treat it like it is phishing until proven otherwise, rather than trusting it.
Companies that have a relationship with a managed IT provider give their employees another resource they can go to for help checking the validity of a suspicious email.
The technology experts at Haxxess can put anti-phishing protocols in place that help protect your data and combat the rise in phishing attacks.
Contact us today to schedule a free consultation! Call 705-222-8324 or reach out online.