How hackers are working around 2 factor authentication checks.
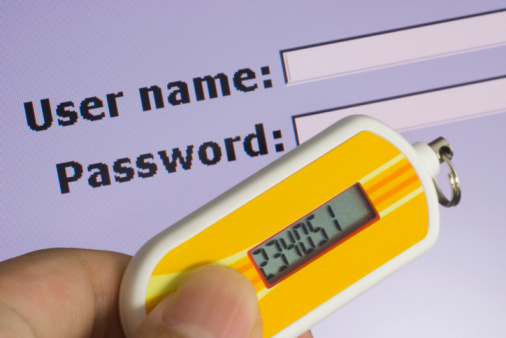
2FA (2 factor authentication) checks were developed to give one certainty that the account is secure since it uses more than password and username credentials. However, hackers have figured out a way to work around the process and steal information (especially if one isn’t paying attention). With this being said, here’s a look at how hackers are mimicking the 2FA process and stealing information.
How Hackers Mimic 2FA Access
When using credentials related with a massive database (such as LinkedIn or Twitter), it’s much easier for a hacker to pose as a company. For example, if a hacker claims to be Twitter through a phishing email containing malicious content that installs a keylogger on the box, the credentials are sent back to the hacker (as opposed to Twitter headquarters).
Once the hacker has your information, they send a message (i.e. a text message) pretending to be the company in question. The message claims that “suspicious” activity is associated with the account, so a 2FA code is being sent to avoid having the account locked. Once the hacker has the credentials in question, the hacker can log into the account with the information and can enter the private 2FA code.
How To Avoid 2FA Attacks
First off: if you see something, say something. Let friends and coworkers know of this threat so their information doesn’t fall into the wrong hands. If one has accounts that are protected by a 2FA system, the only time one will ever be sent a verification is if someone is trying to log into the account in question. Under no circumstance would a user randomly receive a verification code. If so, it’s likely a scammer who is attempting to access an account with the password and username information.
To stay further in the clear, never give a verification code to anyone. The only time one should use a 2FA login procedure is if one is accessing the said account. Never give out personal information (such as credit card information or a Social Security number) in response to an email or text message as one never knows who is on the other end of the device.
Considering the information above, it’s very important that one doesn’t provide your information without reason. Thankfully, Haxxess Enterprise Corporation is the trusted choice when it comes to staying ahead of the latest information technology tips, tricks, and news. Contact us at (705) 222 -TECH or send us an email at [email protected] for more information.